
Why I Advise Our Retail Edge Customers to Choose Docker Over Kubernetes
In my role at Acumera, I work closely with retail, convenience store, QSR, and fuel operators to design edge strategies

Secure Remote Access to POS, ATG, DVR, and More: A PCI Assessor’s Take on Saving Time, Cutting Costs, and Staying Compliant
Even with the increasing number of people working remotely and the reliance on third-party technicians, with the right solution, you can still enable them to securely connect to POS, DVR, ATG and other inherently insecure devices in a PCI compliant manner.

What Multi-Site Retail Can Learn from QSRs About Edge Computing and Network Visibility
Over the years, I’ve worked with both retailers and Quick Service Restaurants (QSRs), and one thing is clear: QSRs cracked

Understanding Managed Broadband Services | Acumera
Managed Broadband Services: How They Work and Their Benefits In today’s digital-first world, businesses rely heavily on robust broadband networks

How to Choose a PCI DSS Level 1 Service Provider: A Practical Guide for 2025
Organizations can improve their compliance status and reduce the internal burden of compliance by carefully choosing PCI compliant service providers. Selecting the right provider for your company requires careful attention to detail since there is a wide variety of service providers and levels of services they offer. This guide is intended to assist you in that evaluation process.
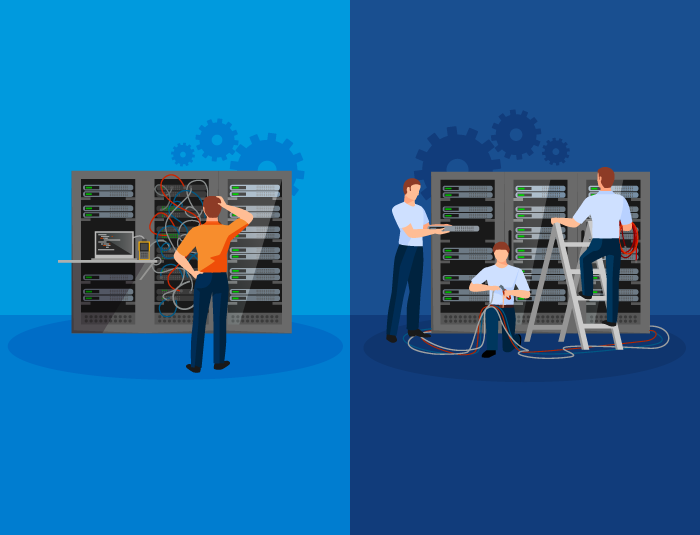
DIY vs. Managed Services for Multi-Site Retail Networks: A Network Engineer’s Perspective
Before I joined Acumera, I worked as a contractor supporting IT infrastructure for multi-site businesses—quick-serve restaurants, convenience stores, fuel stations,

How Acumera® is Transforming Restaurant Technology with Edge Computing
When managing a restaurant’s technology stack, edge computing might not be the first thing that comes to mind. However, this

What is Network Penetration Testing? Internal vs External
In today’s cybersecurity landscape, organizations face an increasing number of sophisticated cyber threats. Protecting sensitive data and systems requires proactive

Essential Guide to Site Preparation for Managed Network Service Provider Installations
When embarking on a Managed Network Service Provider (MNSP) installation, the significance of a site survey and preparation cannot be